Migrating to Cloud? Secure Your Hybrid Cloud with Trend Micro
The COVID-19 crisis has created a massive rush towards cloud adoption. Business interest in cloud-driven tools, apps, and services has reached nosebleed levels. Despite the unprecedented demand for them, the cloud services offered by major platforms have, by and large, offered seamless migration, operation, and business continuity, enabling businesses to thrive despite the crisis.
As organizations migrate from their on-premises infrastructure to a cloud or hybrid one, their security posture must evolve to meet the changing reality.
If businesses have any doubt that the coronavirus is going to slow or hinder the activities of hackers, then the recent DDoS attack on the US Department of Health and Human Services should instantly evaporate those doubts.
They are not stopping, which means that businesses are looking at an uphill task to secure their infrastructure. That’s one of the reasons why businesses are choosing cloud over on-premises. However, a time of crisis like the present one poses its own challenges. The pandemic has created a conducive environment for a number of cyber threats. Here’s how:
- DDoS Attacks
As more businesses migrate to the cloud, the ROI for hackers to attack the same cloud platform increases. The fact that it’s already dirt-cheap to mount a DDoS attack ($5 for a 5-minute attack) does not make things any better. Therefore, cloud security is more important than ever.
- Phishing
Endless virtual meetings, overworked employees, and a whole new set of digital collaboration tools – that’s the life of an employee working from home during the pandemic. They are struggling to learn how to use the tools, often on their personal devices with questionable security. All of these factors make them more vulnerable to phishing attacks and even malware attacks. Their compromised devices can act as conduits for the attackers to gain access into the corporate IT infrastructure.
- Ignored Assets
Dormant virtual servers, physical servers without the latest updates installed, and hybrid infrastructure without proper configurations are all sitting ducks for hackers. As businesses scramble to avoid business disruption and ensure business continuity, these things can often get ignored, resulting in a hacker gaining access to these systems.
What About Security Features Offered by Cloud Service Providers?
Cloud security is a shared responsibility between cloud service providers and their customers. Infrastructure as a Service Cloud Providers like Azure, AWS, and Google Cloud do offer robust features that bolster their infrastructure’s security posture. DDoS protection, penetration testing, secure storage, and several other features vastly improve the security of their platforms. However, their security features are only one part of the puzzle. Once a customer gains access to their infrastructure, everything IN the cloud is the responsibility of the customer. Their data, apps, workloads, OS, and everything else requires appropriate security, which is not the domain of cloud infrastructure service providers. And, this is precisely where several businesses find themselves in the deeper end of the pool for several reasons, as follows:
– Lack of expertise in cloud or infrastructure security
– Blind spots. It’s not always easy to document and follow up on the security best practices to be followed for every aspect of the systems on the cloud
– Increased difficulty in implementing all security features due to lockdown restrictions on personnel movement
– Continued access to employees even when not needed, leading to insider attacks
The Solution: Cloud Security Automation with Trend Micro
Considering that human errors are the leading cause of security breaches in organizations, security experts are turning to automation wherever and whenever possible.
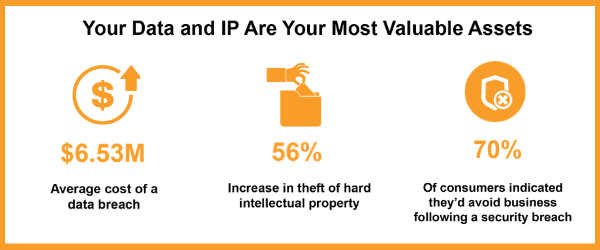
 .
.
Trend Micro Cloud One™ is designed to shoulder the bulk of the cloud security needs of a business efficiently. It integrates into your cloud, automatically identifies the workloads on it, and optimizes the runtime security seamlessly. It’s highly scalable and utilizes your cloud infrastructure to boost the performance of its real-time security services drastically.

There are several more advantages of the sophisticated security offered by Cloud One™. Here are some of them:
– Quick start deployments, including Cloud Formation templates (AWS) and PowerShell scripts (Azure) for automated provisioning and deployment
– Easy integration with all major cloud services providers
– Automation addresses the skill shortage and eliminates a bulk of human errors
– Reduced budget and overhead for support and maintenance tasks
– Advanced security capabilities against vulnerabilities and emerging threats
– Consistent and streamlined protection across hybrid, cloud, and on-premises systems
Secure Your Cloud with AsiaPac
AsiaPac has been at the forefront of providing proven security solutions for businesses in Singapore for decades. Our clients depend on us to reinforce their security posture, improve their preparedness against potential security incidents, and minimize the impact of any security breaches on their business operations. AsiaPac’s partnership with Trend Micro is the next logical step in that commitment to help businesses secure their IT infrastructure.
The sense of urgency towards cloud migration created by the COVID-19 pandemic is not complemented by the proportional availability of cloud skills in the market. Therefore, businesses must rely on security automation and optimization to protect their cloud systems. AsiaPac is uniquely positioned to analyze, understand, and recommend security solutions that address the specific security needs of each business’s cloud migration, integration, and utilization projects.
Looking to the Future.
To learn more about Trend Micro Cloud One™’s features and understand its relevance in today’s business environment, visit Trend Micro Cloud One™ Webinar Series.
To access and try out a FREE Security Assessment, click here.
To understand how Cloud One™ can benefit your organization thoroughly, and help you protect your IT infrastructure against advanced cyber threats, get in touch with us by clicking here.
Tags: Antivirus, AWS, Cloud Consultancy, Cloud Migration, Cloud One, Cloud Protection, Cloud Security, Cloud Security Automation, Cloud Service Providers, Cyber threats, Data Security, DDOS, Hybrid cloud, Managed Cloud Services, Microsoft Azure, Phishing, SMB, Trend Micro,
Other blog posts you might be interested in:
Trending posts
- Benefits of Proactively Monitoring your IT Networks
- A Guide to Proactive Anti-Ransomware Strategy
- 5 Tips to Help Your Business Benefit from Cloud Storage in 2022
- Migrating to Cloud? Secure Your Hybrid Cloud with Trend Micro
- HPE VDI-as-a-Service: Overcoming Business Continuity Threats in a Rapidly Evolving World
- Dynatrace on AWS: The Eagle Eye Into Your Cloud Environments
